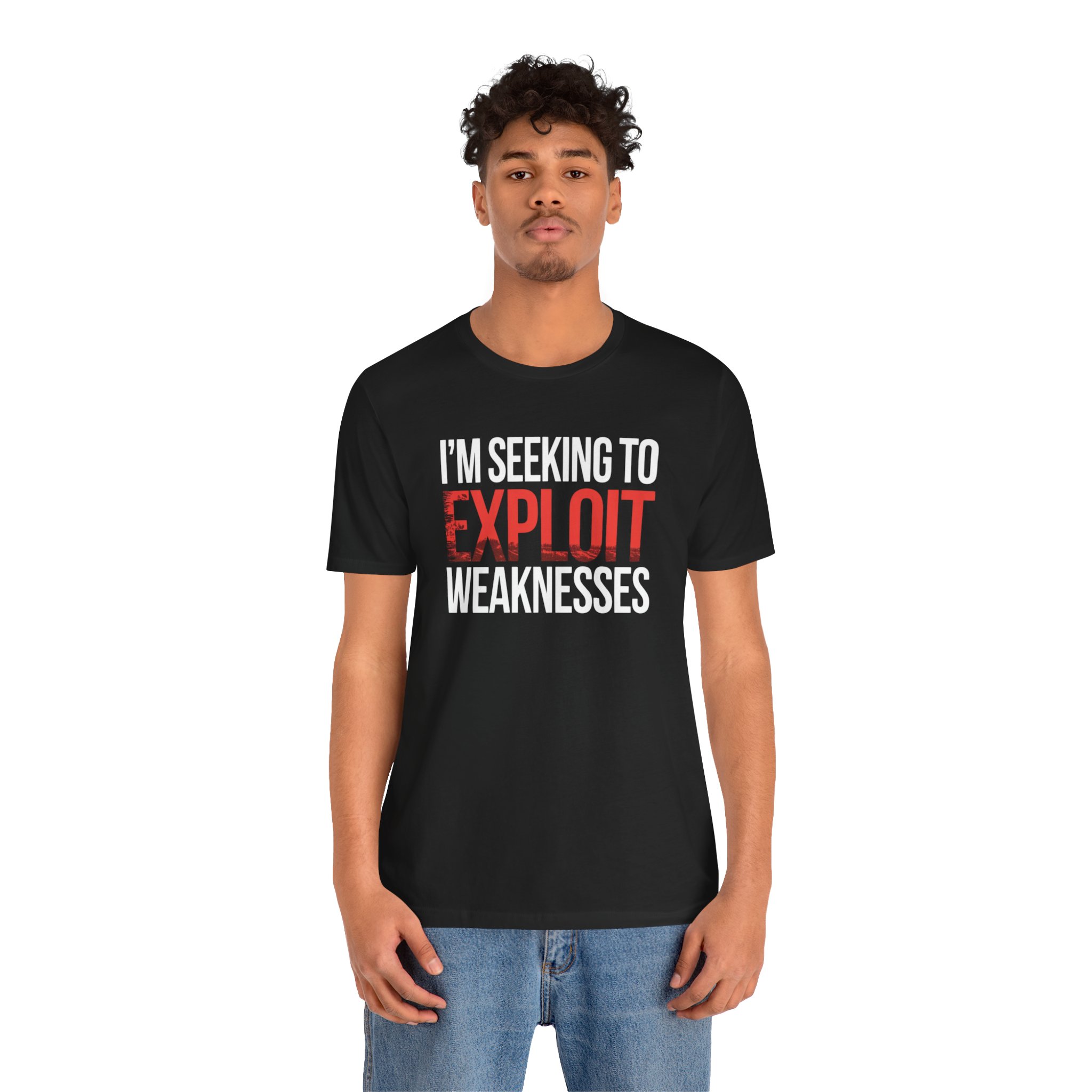
Seeking to Exploit Weaknesses T-Shirt
Hacker Culture — Unisex Tee
Product Description:
Bold white and red typography fills the chest with a statement that reads like a threat assessment: “I’M SEEKING TO EXPLOIT WEAKNESSES.” The word “EXPLOIT” is rendered in distressed red, adding visual aggression to an already confrontational message.
In cybersecurity, exploitation is a science. Finding the vulnerability is research; exploiting it is proof that the risk is real. This tee speaks the language of penetration testers and red team operators who spend their careers identifying what others missed. The direct, unapologetic phrasing mirrors the way vulnerabilities are documented in assessment reports — clinical, factual, and impossible to ignore.
For offensive security professionals, bug bounty hunters, and vulnerability researchers who turn weaknesses into lessons. Also works as fair warning to anyone within reading distance. Available in multiple colors and sizes XS through 5XL.
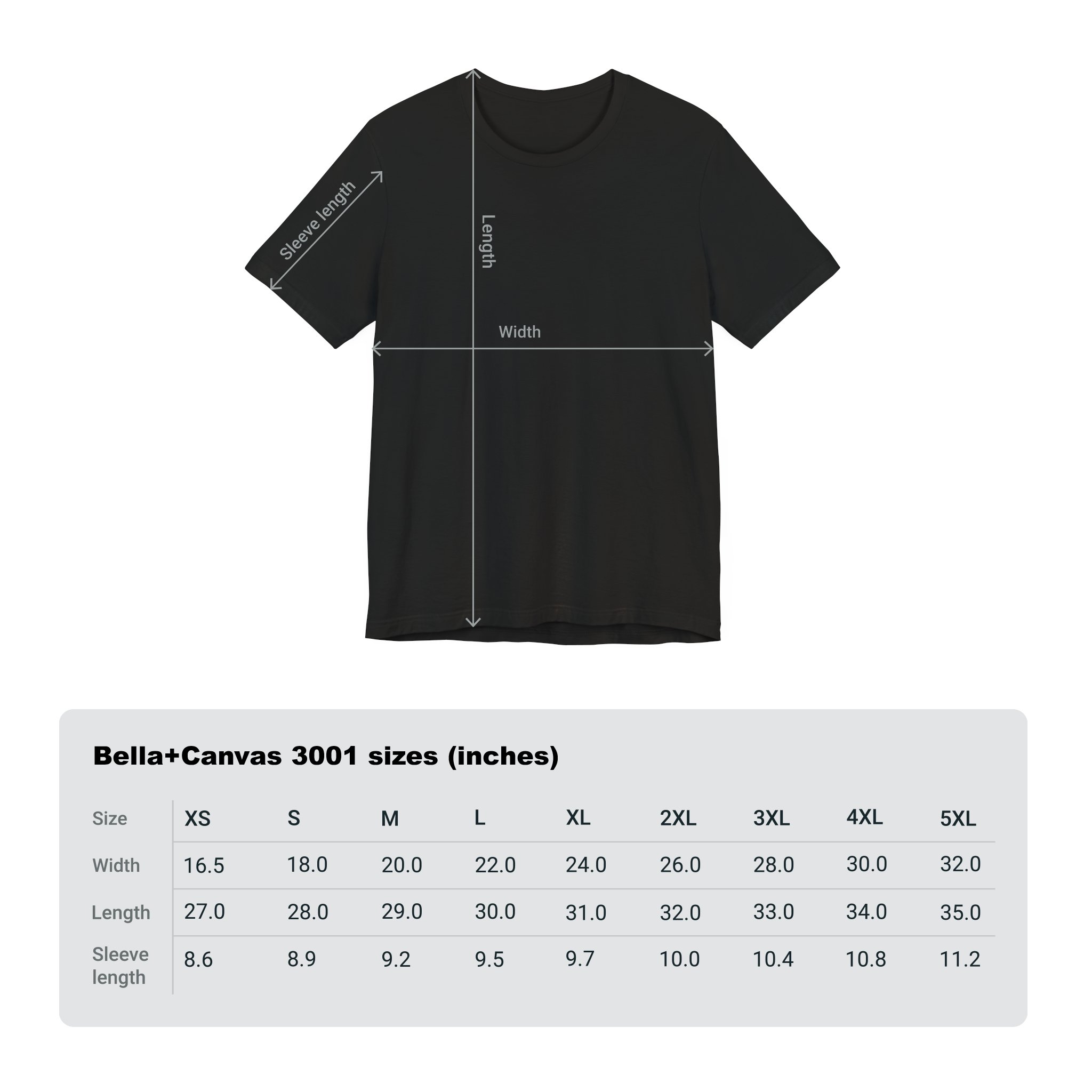
T-Shirt Specifications
- 100% Airlume Combed and Ringspun Cotton: Super soft and comfortable for all-day wear.
- Light Fabric (4.2 oz/yd² | 142 g/m²): Breathable and easy to layer for any season.
- Retail Fit: Designed to look great on all body types.
- Tear Away Label: No itchy tags — pure comfort.
- Runs True to Size: Order your usual size for a familiar fit.
Care Instructions: Machine wash cold, tumble dry low. Do not bleach.